American security researchers from the University of Maryland and Northeastern University have conducted a joint project to study the issues that arise when concluding smart contracts between users of the Ethereum platform. Compared to other blockchains, smart contracts are three times more often created on the basis of other contracts in Ethereum.
Table of Contents
The study’s key findings
The researchers in their study used a software tool based on the Geth console client that allows you to view bytecodes of smart contracts recorded in Ethereum. Information was extracted from the first 5 million blocks generated on the Ethereum blockchain during the first 3 years of its operations.
In a detailed study of the contents of the blocks, it became clear that 60% of the smart contracts created were never subsequently concluded. This means that the network is loaded with a large amount of unnecessary information and useless tokens.
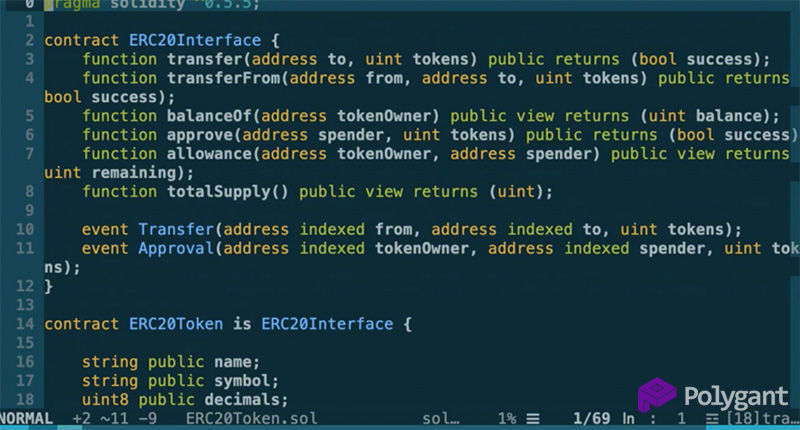
Researchers also found out that only 10% of smart contracts are unique, written from scratch. The remainder were either created according to an existing template or the partial use of a borrowed code. The low diversity of smart contracts, the massive copying of someone else’s code, and multiple bugs degrade the security of the entire Ethereum platform.
Identical code in terms of security
Multiple records in blocks of the same content may be convenient and justified when you need to create many of the one-type smart contracts using the same template. This practice, however, can lead to the spread of vulnerability or an error that occurred in one record to thousands of others.
The American researchers recalled high-profile cases in which hackers exploited vulnerabilities arising from major bugs:
- In November 2017, a Parity user managed to accidentally freeze 578 other people’s wallets containing 513,000 ETH (~$170 million). These coins became permanently stuck in Ethereum.
- In April 2018, an attacker learned how to replicate 12 types of ERC-20 tokens from scratch, using only an error in smart contracts, and then changing them to ethers through the OKEx exchange. This exchange and HitBTC then suspended deposits and withdrawals of any ERC-20 tokens until Ethereum’s developers fixed the error.
- In October 2018, the hacker stole 165 ETH (~$38,000) from the SpankChain crypto project, finding a vulnerability in the payment channel’s smart contract. This white hacker later returned all the coins, and SpankChain even paid him a reward for the security lesson taught.
Common myth about transaction security
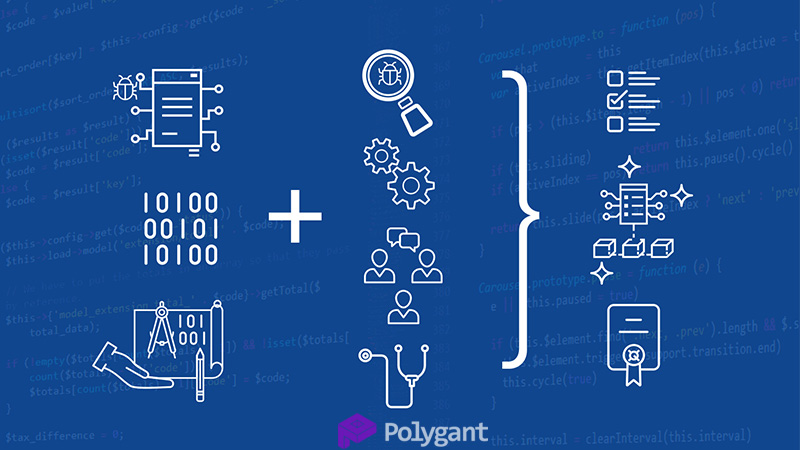
There is a widespread belief that by means of smart contracts it is possible not only to reduce transaction costs by eliminating intermediaries, but also to increase its security. However, according to Jimmy Song, a well-known entrepreneur and developer of Bitcoin Core, this belief is false:
The automatic fulfilment of the terms of the agreement allows us to call the system of smart contracts a powerful payment tool, but it does not raise it to the level of artificial intelligence.
In addition, he said, smart contracts are often written by people who have never seriously engaged in legal practice. Such amateurs seldom understand how to correctly draw up a reliable contract, so it is from this that possible flaws in transaction security arise. But the main thing is that they consider their code to be ideal, not needing an audit.